The "Quick Fix" That Lasts Forever
It starts innocently. A production issue pops up. An engineer logs into the AWS console, clicks “Edit” on a Security Group, and fixes the bug. Fast. Efficient.
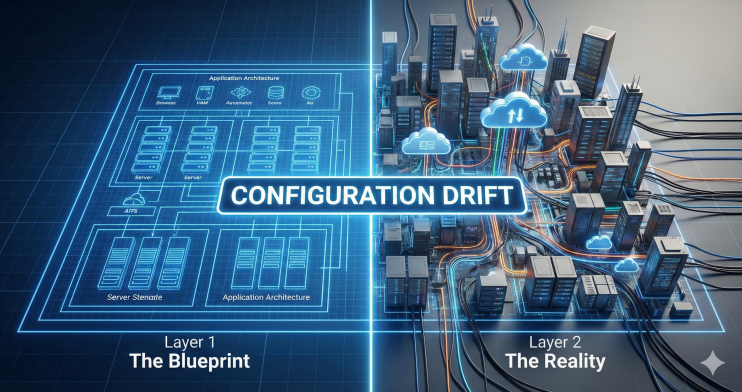
But that manual click just created “Configuration Drift.” Your infrastructure documentation is now a lie. Your Disaster Recovery plan is now broken. And most importantly, that change is untracked.
This is “ClickOps”—the habit of managing cloud infrastructure manually. In 2026, ClickOps isn’t just sloppy engineering; it is financial negligence. Without strict Cloud Governance, manual changes create invisible liabilities.
The Invisible Tax of Shadow IT (Sprawl)
When you allow ClickOps, you invite Cloud Sprawl. Without the guardrails of IaC, engineers spin up resources that are never spun down. We recently audited a client who believed they had 50 staging environments. The audit found 85. Why? Because 35 “quick experiments” were spun up manually 6 months ago and never spun down.
Without Infrastructure as Code (IaC), there is no “Delete” button for the organization. There is only accumulation. IaC (using tools like Terraform or OpenTofu) forces every resource to have a lifecycle. If the code is deleted, the resource dies. It is self-cleaning.
IaC is a Financial Tool, Not a Dev Tool
Most C-Level leaders think IaC is about “developer speed.” It isn’t. It is about Auditability. It is a fundamental pillar of Cloud Cost Optimization. You cannot optimize what you cannot track
Financial Control: With IaC, every cost increase is visible in a “Pull Request” before it happens. You can see: “Added: 2 x p3.2xlarge instances.”
Disaster Recovery: If your region goes down today, can you rebuild your entire company in 1 hour? With ClickOps? Impossible. With IaC? It’s one command:
terraform apply.
If your infrastructure isn't defined in code (IaC), you don't own it—you're just borrowing it from the console. Read why IaC is non-negotiable for enterprises. Take the Governance Maturity Test Now. #DevOps #CloudGovernance #IaC #CTO #Terraform
The "No-Console" Policy
The most mature organizations we work with implement a “Read-Only Console” policy. Human engineers can look at the production console, but they cannot touch it. All changes—even emergencies—must go through code pipelines.
This sounds extreme. It is actually the only way to sleep at night.
Conclusion: Code is Truth
If your infrastructure exists only in the minds of your senior engineers, you are one resignation away from chaos. Make IaC non-negotiable. Because if it’s not in code, it doesn’t exist.
Eliminate Shadow IT and regain control of your cloud assets.
Understanding that “ClickOps” is a financial liability is step one. Step two is identifying exactly how deep your Shadow IT sprawl actually goes.
We use a proprietary Cloud Governance Framework at GYSP to help enterprises lock down their consoles, eliminate manual drift, and turn their infrastructure into a highly auditable financial ledger.
Stop guessing who is spinning up expensive resources. Use the exact diagnostic tool we use with our enterprise clients to measure your IaC maturity and find your governance blind spots.
Take the IaC Governance Assessment Below 👇





This hits home. We spent 3 months last year just tagging ‘orphaned’ resources from previous employees who loved ClickOps. But here is the friction point we face: Emergencies. My team pushes back on a strict ‘Read-Only Console’ policy because they argue, If the site is down at 3 AM, I can’t wait 10 minutes for a Terraform pipeline to apply a fix. How do you handle ‘Break Glass’ scenarios without destroying the IaC culture?